Google Quantum AI says it can break Bitcoin in 9 minutes. Should we actually worry?
500,000 physical qubits, 9 minutes. The paper that turned the quantum threat into concrete numbers
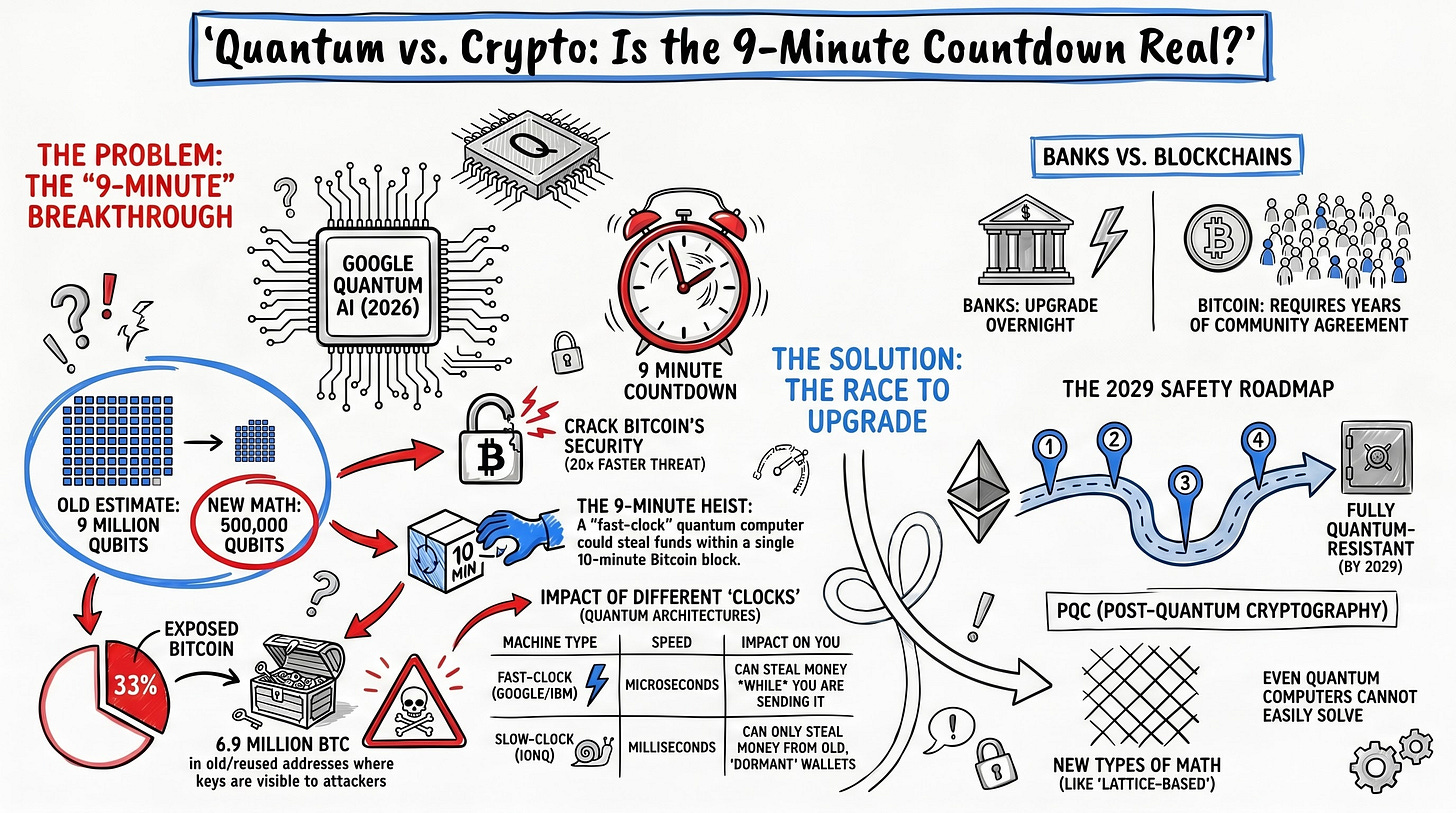
On March 31, 2026, the Google Quantum AI team released a 57-page whitepaper. The core finding: the quantum resources needed to solve the 256-bit Elliptic Curve Discrete Logarithm Problem (ECDLP-256), which underpins cryptocurrency security, have dropped roughly 20x compared to prior estimates. Specifically, 1,200 logical qubits and fewer than 500,000 physical qubits would be enough to derive a Bitcoin private key within minutes. This article breaks down the whitepaper’s main claims, the differing vulnerability structures of Bitcoin and Ethereum, the companies and foundry ecosystems behind each quantum hardware platform, and what a Post-Quantum Cryptography (PQC) transition means for the crypto value chain.
Contents
Intro: Why this paper matters
Background: quantum computers and ECDLP, from the basics
The Google whitepaper in detail: 1,200 logical qubits, 9 minutes
Bitcoin vs Ethereum: vulnerability structures are not the same
Quantum hardware platforms and the main players
The “dormant coin” problem and digital salvage
The state of the Post-Quantum Crypto ecosystem
Closing
References & Sources
1. Intro: Why this paper matters
On March 31, the Google Quantum AI team published a whitepaper titled “Securing Elliptic Curve Cryptocurrencies against Quantum Vulnerabilities: Resource Estimates and Mitigations.”[1] Ryan Babbush (Director of Research, Google Quantum AI) and Hartmut Neven (VP of Engineering, Google Quantum AI) are the lead authors, with Justin Drake (Ethereum Foundation) and Dan Boneh (Stanford) among the co-authors.
Here’s why this matters. Up to now, the “quantum computers will break Bitcoin” narrative has floated around on vague timelines and unverified numbers. This paper is different. It provides concrete quantum resource estimates while making those estimates cryptographically verifiable through a zero-knowledge proof. The details of the attack stay hidden, but the credibility of the estimates is mathematically backed. In the field of quantum cryptanalysis, this kind of responsible disclosure is essentially a first.
The market reacted immediately. Quantum Resistant Ledger (QRL) +50%, Cellframe (CEL) +40%, Abelian (ABEL) +25%.[2] Bitcoin and Ethereum themselves moved only modestly. The price action reflects a very specific message: “Not dangerous right now, but whoever isn’t ready is going to have a problem.”
In this piece, I’ll walk through the technical substance of the paper, how Bitcoin and Ethereum differ in their quantum vulnerabilities, which companies are building the hardware (and which foundries they lean on), and what the PQC transition implies for the crypto value chain.
2. Background: quantum computers and ECDLP, from the basics
Most cryptocurrencies, Bitcoin and Ethereum included, rely on Elliptic Curve Cryptography (ECC). Specifically, the security backbone is the Elliptic Curve Discrete Logarithm Problem (ECDLP) defined over the secp256k1 curve.[1]
Put simply: generating a public key from a private key is easy, but inverting that operation to recover the private key from the public key is, for classical computers, effectively impossible. That asymmetry is what underwrites ownership in the system. “Only I can spend my coins” rests on that one-way math.
One thing worth clarifying. This asymmetry isn’t “mathematically impossible,” it’s “computationally infeasible.” Breaking 256-bit ECDLP on a classical computer would take longer than the age of the universe. But Shor’s Algorithm, introduced by Peter Shor in 1994, showed that a quantum computer can solve this problem in polynomial time.[1]
The question has always been “when.” Actually running Shor’s algorithm requires enough error-corrected logical qubits (stable qubits built from hundreds of physical qubits each), and the most advanced quantum processor today, Google Willow, has only 105 physical qubits.[3] That’s why the industry consensus has been “still far away.”
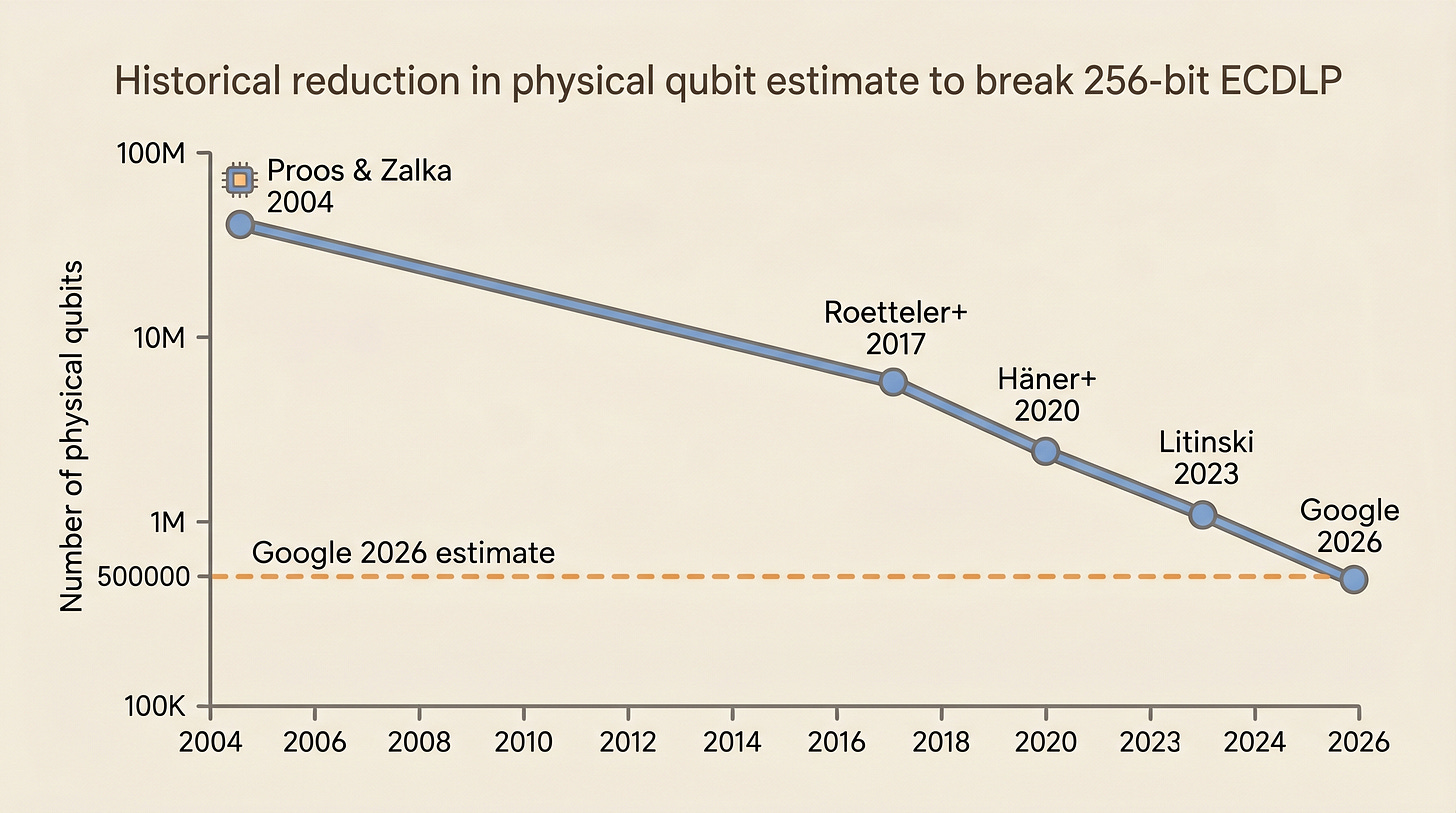
Timeline of ECDLP-256 quantum resource estimates
The Google paper just pulled that timeline in significantly.
Bottom line: the physical qubit count needed to break ECDLP-256 dropped from the prior best estimate of around 9 million to under 500,000, roughly a 20x reduction.
3. The Google whitepaper in detail: 1,200 logical qubits, 9 minutes
Resource estimates: two circuit variants
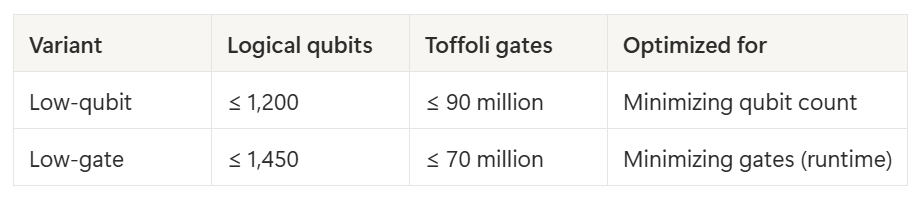
The Google team’s main result is two quantum circuit variants.[1]
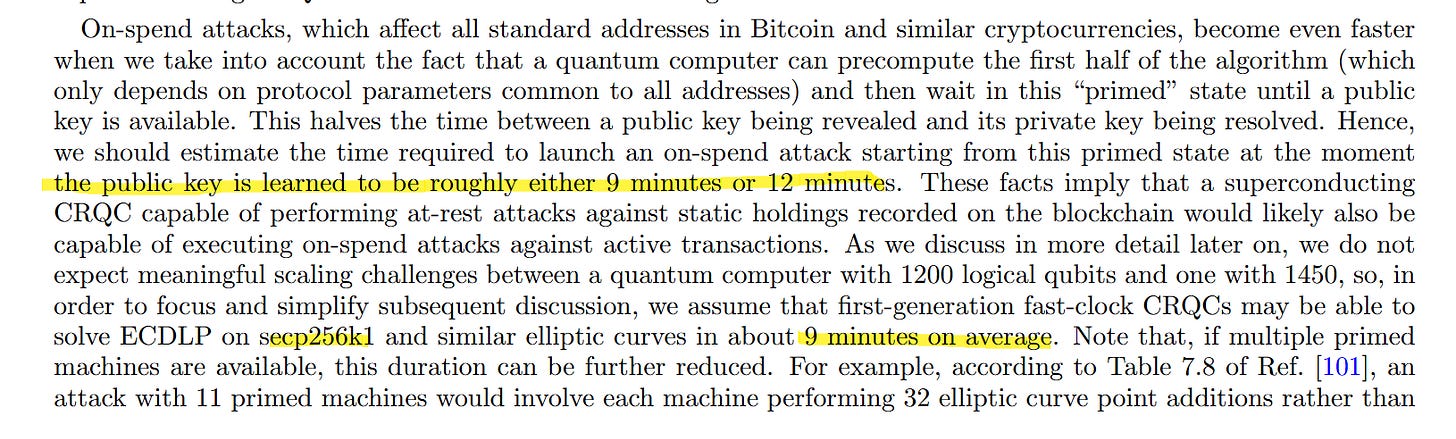
The Toffoli gate count (Toffoli being the most expensive basic operation in fault-tolerant quantum computing) determines execution time. On a surface-code based superconducting qubit architecture, assuming a 10-microsecond error correction cycle reaction time, 70 million Toffolis take about 18 minutes, and 90 million take about 23 minutes.[1]
One more detail. Shor’s algorithm lets you precompute the first half of the calculation (the part that depends only on protocol parameters) and hold that “primed state.” Once a public key is exposed, you only run the second half. That brings the real attack time down to about 9 minutes.[1]
Bitcoin’s average block time is 10 minutes. At 9 minutes, the probability of a successful attack is roughly 41%.[1]
Verification through a Zero-Knowledge Proof
This is the most unusual part of the paper. The Google team did not publish the detailed structure of the quantum circuits. Instead, using the SP1 zero-knowledge virtual machine (zkVM), they issued a ZK proof that verifies “we possess a circuit of this size, and this circuit correctly computes point addition on the secp256k1 elliptic curve across 9,000 random inputs.”[1]
Why this approach? The paper explains it directly. The quantum cryptanalysis field has an odd culture. Developing and optimizing quantum algorithms is academically prestigious, but discussing the downstream consequences of those algorithms is often treated as taboo.[1] The Google team takes the position that it’s time to move past that. Keep the attack details private, but make the scale of the threat cryptographically verifiable. This is the first time the “Responsible Disclosure” principle from traditional security has been applied to quantum cryptanalysis.
Fast-clock vs Slow-clock: architecture determines attack type
The paper’s other key contribution is classifying quantum computer architectures by “clock speed” into two categories.[1]
Fast-clock CRQC (Cryptographically Relevant Quantum Computer): Superconducting, photonic, silicon spin qubits. Error correction cycles around 1 microsecond. Can solve ECDLP in minutes, making on-spend attacks (intercepting in-flight transactions) viable.
Slow-clock CRQC: Neutral atoms, ion traps. Fundamental operation speed 100 to 1,000x slower than fast-clock. Solving ECDLP takes hours to days, so only at-rest attacks (targeting dormant wallets with long-exposed public keys) are viable.
Don’t read this as “Fast-clock is the better quantum computer.” Fast vs Slow refers to the error correction cycle speed, not to qubit quality or scalability. Ion traps (Slow-clock) actually hold the world record for gate fidelity across all architectures, and neutral atoms have the edge in scaling qubit counts quickly.[1] Superconducting (Fast-clock), by contrast, has fast gates but limited qubit connectivity and requires millikelvin cryogenics. The paper introduces this distinction not to rank architectures, but to analyze what kind of attack the first CRQC will be able to execute.
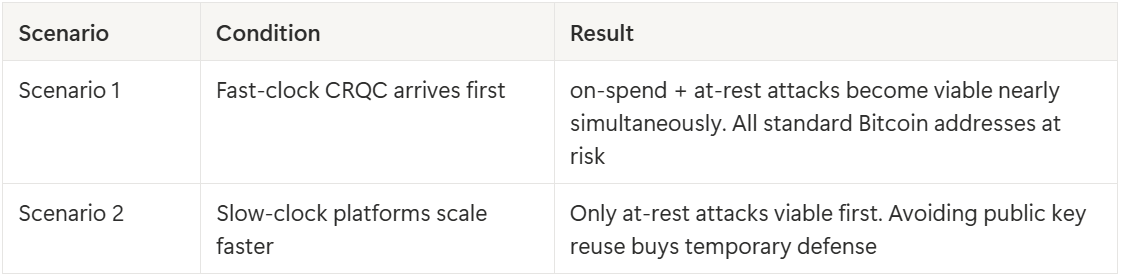
Why does the distinction matter? Because the nature of the shock hitting the crypto ecosystem depends entirely on which architecture produces the first CRQC. The paper lays out two scenarios.[1]
Bottom line: The Google paper converts the old “someday quantum will be a threat” conversation into something concrete: “500,000 physical qubits, 9 minutes,” plus architecture-specific scenarios.
4. Bitcoin vs Ethereum: vulnerability structures are not the same
When talking about quantum threats, lumping “all crypto is at risk” together is a mistake. Bitcoin and Ethereum have fundamentally different designs, and their quantum vulnerabilities differ accordingly.
Bitcoin: risk depends on the script type
Bitcoin uses the UTXO (Unspent Transaction Output) model. Coin ownership is defined by a locking script, and depending on the script type, when and how the public key gets exposed varies.[1]
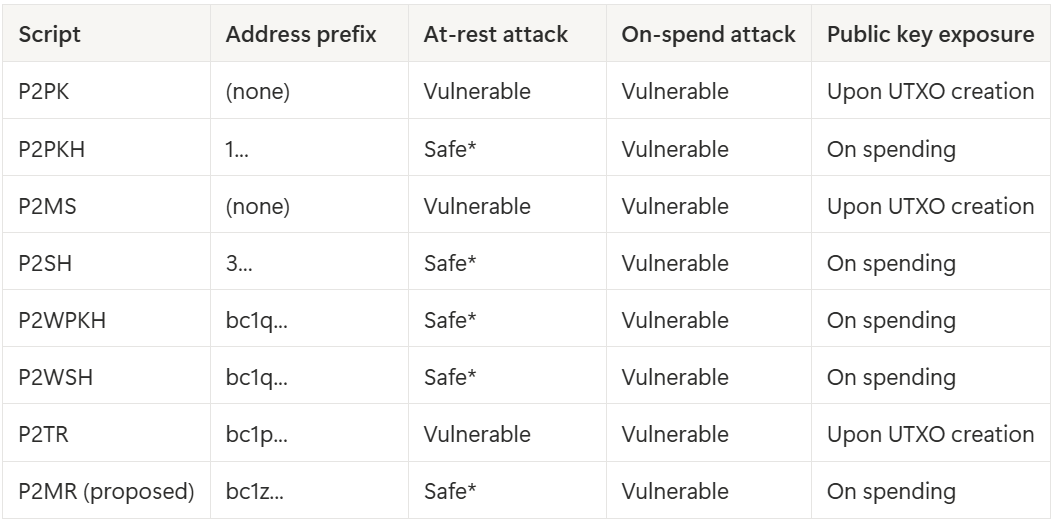
Based on Table I of the whitepaper, here’s the vulnerability breakdown by Bitcoin script type.[1]
*Safe only if no address reuse. Any reuse writes the public key on-chain and converts Safe to Vulnerable.
The key points:
P2PK (Pay-to-Public-Key): The public key is written directly into the locking script. Vulnerable to both at-rest and on-spend attacks. About 1.7 million BTC is locked this way, including Satoshi-era mining rewards.[1]
P2PKH / P2WPKH: Only the hash of the public key goes on-chain. The public key is revealed when the coin is spent, so before the first spend, at-rest attacks can’t touch it. On-spend attacks are still possible.
P2TR (Pay-to-Taproot): Introduced by the 2021 Taproot upgrade, P2TR exposes the public key directly in the locking script. Privacy and efficiency gains, but a regression to P2PK-level exposure from a quantum security standpoint.[1] As of 2025, 21.68% of Bitcoin transactions used P2TR.[1]
Address reuse: Even with hash-based scripts like P2PKH or P2WPKH, if you spend part of the coins at an address and leave the rest, the public key ends up on-chain. At-rest immunity is gone from that moment. The paper notes that major exchanges like Binance, Robinhood, and Bitfinex reuse addresses heavily.[1]
Overall, about 6.9 million BTC (roughly 33% of total supply) is currently vulnerable to at-rest attacks.[1]
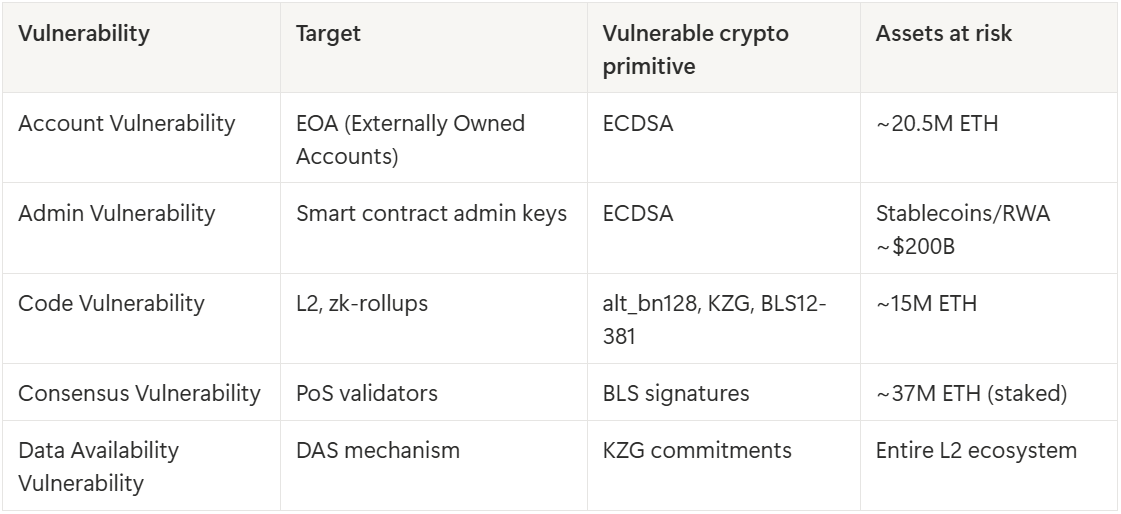
Ethereum: five attack vectors
Ethereum’s quantum vulnerabilities are far more complex than Bitcoin’s. If Bitcoin is a “digital ledger,” Ethereum is closer to a “world distributed computer,” and the attack surface is correspondingly larger.[1]
The paper classifies Ethereum’s vulnerabilities into five categories.[1]
The one that caught my attention most is Admin Vulnerability. Stablecoin issuers (USDT, USDC, etc.) protect minting authority with ECDSA-based admin keys. Break one of those keys and you can mint unlimited tokens, which would cascade into every DeFi lending market using those tokens as collateral.[4]
Another one worth noting is Data Availability Vulnerability. Ethereum’s DAS (Data Availability Sampling) mechanism depends on KZG commitments, which are vulnerable to on-setup attacks. Once a quantum computer recovers the “toxic waste” (the secret values that were supposed to be destroyed during the trusted setup ceremony), classical computers alone can forge data availability proofs from that point forward. The paper calls this attack “potentially tradable”, meaning a one-time quantum computation produces a reusable exploit that can be sold.[1][4]
Ethereum does have some advantages over Bitcoin here. The 12-second block time (vs Bitcoin’s 10 minutes) makes on-spend attacks much harder even for fast-clock CRQCs under current estimates. And the ecosystem already has substantial private mempool infrastructure like TEE-based BuilderNet (private mempool: submitting transactions directly to trusted block builders instead of the public queue).[1]
Bottom line: Bitcoin’s key variable is script type; Ethereum has five distinct attack vectors spanning the account model, smart contracts, PoS, and DAS. “Crypto is all at risk” is too coarse.
So what about traditional finance?
A natural question at this point: “If quantum computers break ECDLP, isn’t banking, SWIFT, and HTTPS all going down too, not just Bitcoin?” Fair point. This was the most common pushback from the crypto community after the paper dropped. CZ (Binance founder) posted on X that “all crypto has to do is upgrade to Quantum-Resistant algorithms. No need to panic,”[20] and crypto commentator Quinten Francois went further: “If quantum kills Bitcoin, it also kills the global banking system, SWIFT transfers, stock exchanges, military communications, nuclear command systems, every HTTPS website on earth.”[20]
Not wrong. TLS (web traffic encryption), SSH (server access), electronic passports, digital signature infrastructure all depend on ECDLP or RSA, and quantum computers threaten all of them.[1]
But here’s what the paper points out head-on. The upgrade dynamics are completely different.
Traditional finance systems are centralized. JP Morgan’s CISO makes a call, the security team swaps TLS certificates, and customers never need to know. Google started its PQC transition back in 2016 and has now published a timeline to migrate all authentication services by 2029.[1] NIST’s PQC standards (ML-KEM, ML-DSA) are finalized, and enterprise adoption roadmaps are rolling out.
Blockchains can’t do that. There’s nobody with a switch that flips the protocol. Changes require community consensus, and without consensus, you get a chain split. Think about how slow Bitcoin governance has been: Taproot alone took years of debate before activation.
And critically, traditional finance has mechanisms to reverse bad transactions. Hacked bank transfers can be recovered through dispute processes. Blockchains are designed around transaction irreversibility. Once assets move via a quantum attack, there’s no recovery path.[1]
Put plainly: quantum threats aren’t unique to crypto. But crypto is the most exposed, not because the cryptography is weaker, but because upgrades are structurally slow and there’s no recovery mechanism when things fail.
Bottom line: Traditional finance relies on the same cryptography, but centralized organizations can upgrade quietly and have transaction reversal mechanisms. Blockchains have neither. Same threat, different exposure.
Before moving to the quantum hardware side, it’s worth sitting with this structural asymmetry. Which architecture produces the first quantum computer changes the character of the shock the crypto ecosystem has to absorb.
5. Quantum hardware platforms and the main players
The Fast-clock / Slow-clock frame from the Google paper isn’t just theory. Which companies are building which architectures right now determines both the type and the timing of the threat crypto will face.
Fast-clock architectures (on-spend attacks viable)
Superconducting qubits
The most mature architecture. Josephson junction based superconducting circuits operating at ultra-low temperatures (~15mK).
Google Quantum AI (GOOGL): The authors of this paper. Processors manufactured at Google’s own fab in Santa Barbara. In late 2024, they achieved verifiable quantum advantage with the 105-qubit Willow chip.[3] Currently at the forefront of quantum cryptanalysis resource estimation.
IBM Quantum (IBM): Own fab at Yorktown Heights. Operating the 156-qubit Heron and 120-qubit Nighthawk processors. Provides cloud access through the IBM Quantum Network with 300+ participating institutions.[5]
Rigetti Computing (RGTI): Own Fab-1 in Fremont, CA. Accessible through AWS Braket and integrated with NVIDIA CUDA-Q.[5]
IQM Quantum Computers: Finland-based, manufactured at VTT cleanrooms. Core participant in EU quantum initiatives. Private.
Photonic qubits
Uses photons as qubits. Photons don’t feel heat or electromagnetic interference, so cryogenic constraints are relatively relaxed, and standard optical fiber allows chip-to-chip networking, which is a big advantage for modular scaling.
PsiQuantum (private, $7B valuation): Runs a dual foundry strategy. High-volume manufacturing of the 300mm Omega silicon photonic chipset happens at GlobalFoundries (GFS) Fab 8 in Malta, NY, on a commercial semiconductor process,[6] while 200mm SiPh development and production ramp runs in parallel at SkyWater Technology (SKYT)‘s Minnesota fab.[18] If GFS is the volume axis, SkyWater is the flexible custom-process axis based on its TaaS (Technology as a Service) model. SkyWater CEO Thomas Sonderman has gone as far as calling his company a “quantum foundry,” signaling just how actively they’re leaning into this business.[19] Breaking ground on data-center-scale quantum compute centers in Brisbane and Chicago. The $1B Series E was led by NVIDIA NVentures, BlackRock, and Temasek, and they’ve advanced to the final stage of the DARPA QBI (Quantum Benchmarking Initiative).[7] If you’re a PhotonCap reader, the GFS silicon photonics platform is familiar territory: PsiQuantum is that platform’s flagship quantum computing customer.
Xanadu (XNDU): Listed on Nasdaq/TSX simultaneously on March 27, 2026, via SPAC merger with Crane Harbor Acquisition Corp. $3.1B valuation.[8] AMD participated in a $275M PIPE, and Xanadu is in negotiations with the Canadian and Ontario governments for up to C$390M.[9] Chip fabrication runs on Tower Semiconductor (TSEM)‘s SiPh platform, where they’ve co-developed a custom SiN-based process and completed multiple tapeouts.[10] imec (Belgium) handles ultra-low-loss SiN wafer R&D, and Applied Materials (AMAT) collaborates on a 300mm process for superconducting TES detectors.[11][12] Target: build a quantum data center in Toronto by 2030.
The photonic quantum foundry landscape is interesting. PsiQuantum is GFS (300mm) + SkyWater (200mm), and Xanadu leans primarily on Tower’s SiPh platform. Foundries that compete in the data-center silicon photonics market are now splitting customers in the new quantum computing demand pool too.
Silicon spin qubits
The big advantage: compatibility with existing CMOS processes.
Intel (INTC): Tunnel Falls 12-qubit processor manufactured at Intel’s Oregon fab. They’re emphasizing CMOS process compatibility and trying to carry over large-scale production know-how to quantum chips.
Diraq (private): UNSW spin-out. Manufactures silicon spin qubit chips on GlobalFoundries (GFS)‘ 300mm process. Also participating in DARPA QBI.
Slow-clock architectures (at-rest attacks only)
Ion traps
Confine individual ions in electromagnetic fields and implement quantum gates with lasers. Gate fidelity is extremely high, but fundamental operation speed is 100 to 1,000x slower than superconducting.[1]
IonQ (IONQ): In 2025, became the first quantum computing company to surpass $100M in annual GAAP revenue.[5] Executed around $2.5B in acquisitions over 18 months, including Oxford Ionics ($1.075B), ID Quantique ($250M), and Capella Space ($318M).[5] Partnerships with NVIDIA, AWS, and AstraZeneca, and a roadmap targeting a CRQC with roughly 20,000 qubits by 2028. Self-manufactured (Maryland).
Quantinuum (private, filed S-1 for IPO): Honeywell subsidiary. Completed a $600M Series B at $10B valuation.[5] Partnerships with NVIDIA NVentures and Microsoft, and recently announced a 800x error reduction demonstration. Self-manufactured.
Neutral atoms
Arrays of individual atoms held by optical tweezers serve as qubits. The strength is rapid qubit count scaling.
QuEra Computing (private): Boston-based. Backed by NVIDIA NVentures, AWS, and Google. Targeting a 100 logical qubit system in 2026.[5]
Pasqal (private): Paris-based. NVIDIA CUDA-Q integration. Deployed at European HPC centers.
Atom Computing (private): Set a record of 24 entangled logical qubits in partnership with Microsoft.[5] Selected for DARPA US2QC.
Infleqtion (INFQ): Formerly ColdQuanta. Listed via SPAC merger in February 2026 at a $1.8B valuation.[5] Runs a dual revenue model combining quantum computing with defense and sensing contracts.
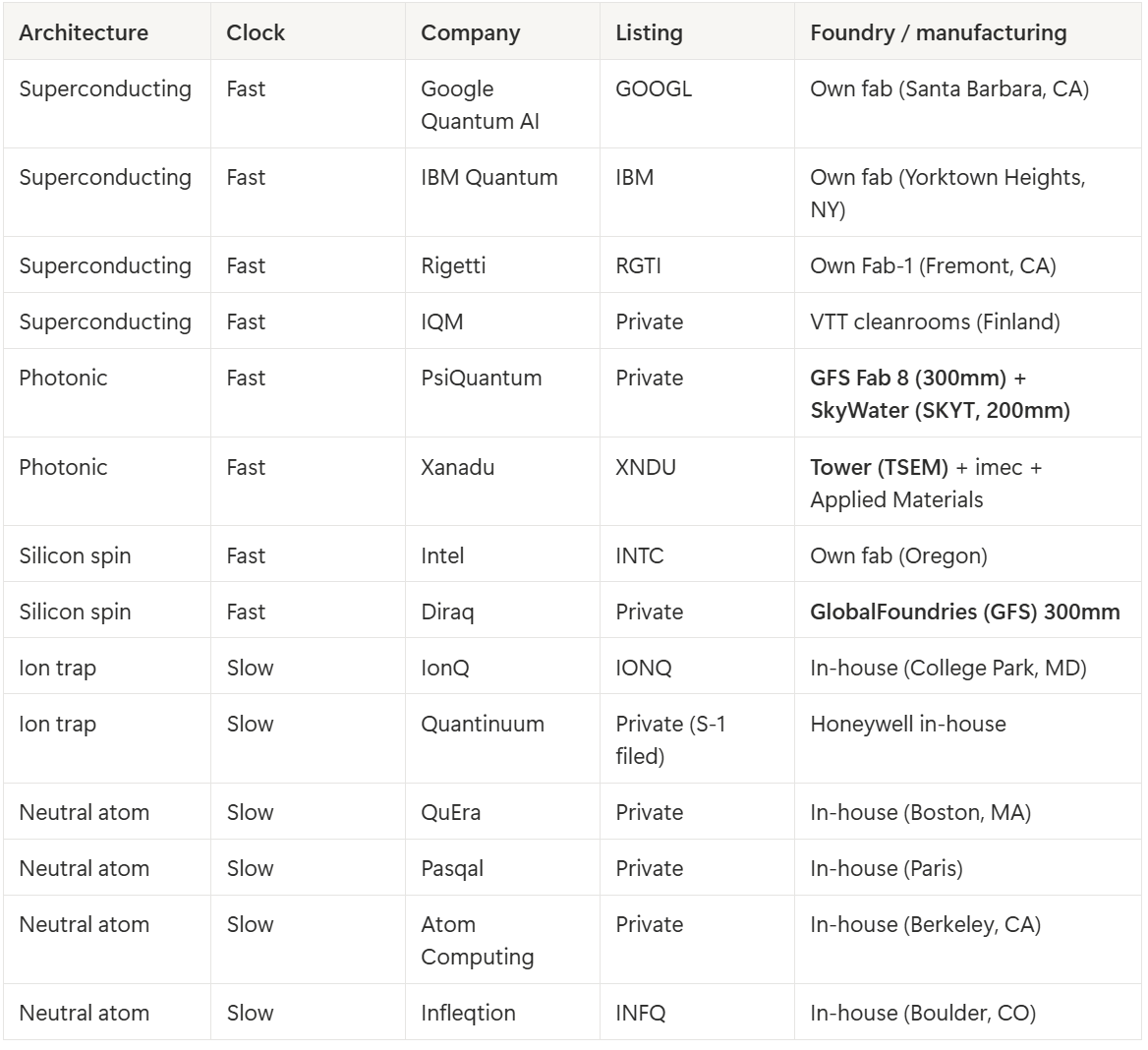
Summary: quantum hardware platforms, companies, and foundries
Here’s a consolidated view of the companies covered above, organized by architecture.
One thing worth flagging from this table. The Fast-clock photonic and silicon spin players lean heavily on commercial semiconductor foundries: PsiQuantum-GFS/SkyWater, Xanadu-Tower, Diraq-GFS. The Slow-clock side (ion trap, neutral atom) mostly manufactures in-house. This isn’t a coincidence. Photonic and silicon spin architectures are compatible with existing CMOS/SiPh processes, while ion trap and neutral atom systems revolve around vacuum chambers and laser systems that have nothing to do with semiconductor fabs.
Cross-platform infrastructure: NVIDIA’s position
NVIDIA (NVDA) doesn’t build its own QPU (Quantum Processing Unit). Instead, it’s running through the entire quantum ecosystem on three axes.
First, NVentures (venture investment): In a single week in 2025, NVIDIA backed Quantinuum (ion trap), QuEra (neutral atom), and PsiQuantum (photonic) consecutively.[13] A portfolio strategy covering every major hardware architecture.
Second, CUDA-Q: A quantum-GPU hybrid programming framework. Lets developers program CPUs, GPUs, and QPUs from a single codebase.[14]
Third, NVQLink: A direct QPU-GPU connection architecture announced at GTC Washington in October 2025. Launch partners include 16 quantum hardware companies (IonQ, Rigetti, Quantinuum, QuEra, etc.) and quantum control system vendors like Keysight and Zurich Instruments.[14]
There’s an episode worth flagging. At CES January 2025, Jensen Huang said quantum computing was “15 to 30 years away from practical use.” A few months later at GTC, he publicly apologized and pivoted NVIDIA’s quantum strategy hard.[15] The surface reading is “Jensen changed his mind,” but personally I’m not sure that was a pure apology. The January comment cooled the whole quantum investment narrative, and a few months later NVIDIA shows up with NVQLink and NVentures investments, effectively broadcasting “even if quantum works, it runs inside the NVIDIA ecosystem.” Slowing the industry down while flexing leverage. Feels more like a calculated sequence than a change of heart.
Bottom line: The quantum hardware foundry/partner ecosystem is already deeply wired into the semiconductor value chain. PsiQuantum-GFS/SkyWater, Xanadu-Tower, Diraq-GFS, and NVIDIA’s cross-platform investment/infrastructure strategy are the key axes.
6. The “dormant coin” problem and digital salvage
The hardest quantum threat problem to solve is “dormant digital assets.”
PQC protects future transactions. But what about coins that have already been sitting on-chain with exposed public keys? Lost private keys, deceased owners, forgotten wallets.
More than 1.7 million BTC is locked just in Bitcoin’s P2PK locking scripts. Counting all script types, vulnerable dormant Bitcoin could reach roughly 2.3 million BTC.[1] At April 2026 prices, that’s tens to hundreds of billions of dollars.
Even if a fork introduces PQC protocols, these assets are “unfixable” fixed targets. A quantum attacker has no time pressure on them.
Community options
The paper lays out three options for the Bitcoin community.[1]
Do Nothing: Take no action. Quantum attackers eventually seize these coins, and a mass sell-off could destabilize the network economy.
Burn: Burn vulnerable dormant coins (make them unspendable). Clashes with Bitcoin’s core principle of ownership inviolability.
Hourglass: Attach an expiration timer to dormant coins. If they aren’t moved to a PQC address within a set period, they’re automatically burned.
Digital Salvage: a new policy framework
Here the paper introduces a genuinely interesting policy proposal: “Digital Salvage.”[1] Analogous to the legal framework for recovering treasure from sunken ships, classify quantum-computer-based recovery of dormant asset private keys as a regulated activity.
Because the legal status of such actions is currently ambiguous, there’s a real risk that nation-state actors or criminal organizations seize these assets first. The paper suggests a “legal backstop” structure: governments legalize salvage while simultaneously recommending that the Bitcoin community voluntarily burn vulnerable coins.[1]
Personally, I think this is the most controversial section of the paper. It collides head-on with Bitcoin’s “code is law” philosophy. But you also can’t ignore the reality that tens of billions of dollars in assets could end up in the hands of criminals or hostile state actors.
Bottom line: Dormant quantum-vulnerable Bitcoin is around 2.3M BTC. A “fixed target” that PQC migration can’t solve on its own. The community and policymakers have to choose from Do Nothing / Burn / Hourglass / Digital Salvage.
7. The state of the Post-Quantum Crypto ecosystem
So how is the response shaping up?
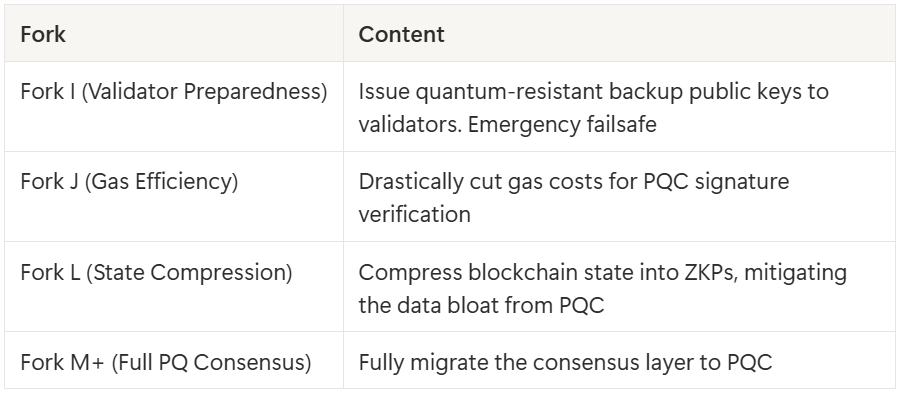
Ethereum Foundation: the 2029 roadmap
On March 24, 2026, the Ethereum Foundation launched pq.ethereum.org, formalizing the Post-Quantum Ethereum initiative.[16] This is the culmination of 8 years of work starting from STARK-based signature aggregation research in 2018.
The roadmap targets L1 quantum resistance by 2029 through 4 hard forks.[16]
The fact that co-author Justin Drake (Ethereum Foundation) participated directly in this paper is itself a signal of how seriously the Ethereum side treats the quantum threat.
Even after L1 protocol upgrades complete, thousands of already-deployed smart contracts, bridges, and L2 protocols each have to upgrade their code and rotate their keys independently.[4] That could take several more years.
Bitcoin: BIP-360
On the Bitcoin side, BIP-360 is under discussion. It would introduce a new script type called P2MR (Pay-to-Merkle-Root) that removes P2TR’s quantum vulnerability (direct public key exposure).[1] But this is mitigation against at-rest attacks only. Stopping on-spend attacks requires replacing the signature algorithm itself with PQC.
Bitcoin’s problem is its governance structure. There’s no central organization that can run a coordinated multi-year engineering program the way the Ethereum Foundation can. The last major cryptographic upgrade, Taproot, took years of debate before activation in 2021.[17] Bitcoin advocate Nic Carter has conceded that “elliptic curve cryptography is on the brink of obsolescence. Whether it’s 3 or 10 years, it’s over and we need to accept that.”[17]
PQC-native blockchains
Some blockchains are built on quantum-resistant cryptography from day one.
Quantum Resistant Ledger (QRL): +50% after the Google paper dropped.[2] Uses XMSS (eXtended Merkle Signature Scheme) hash-based signatures.
Abelian (ABEL): Lattice-based cryptography. +25%.[2]
Mochimo: PQC-dedicated blockchain.
Among existing blockchains, Algorand, XRP Ledger, and Solana have made experimental PQC deployments.[1] Notably, StarkNet uses hash-based SNARKs, which keeps it free from elliptic-curve-based vulnerabilities.[1]
Bottom line: Ethereum has a concrete 2029 roadmap in motion. Bitcoin’s governance structure makes a coordinated response harder. PQC-native chains like QRL and Abelian are starting to earn a market premium.
8. Closing
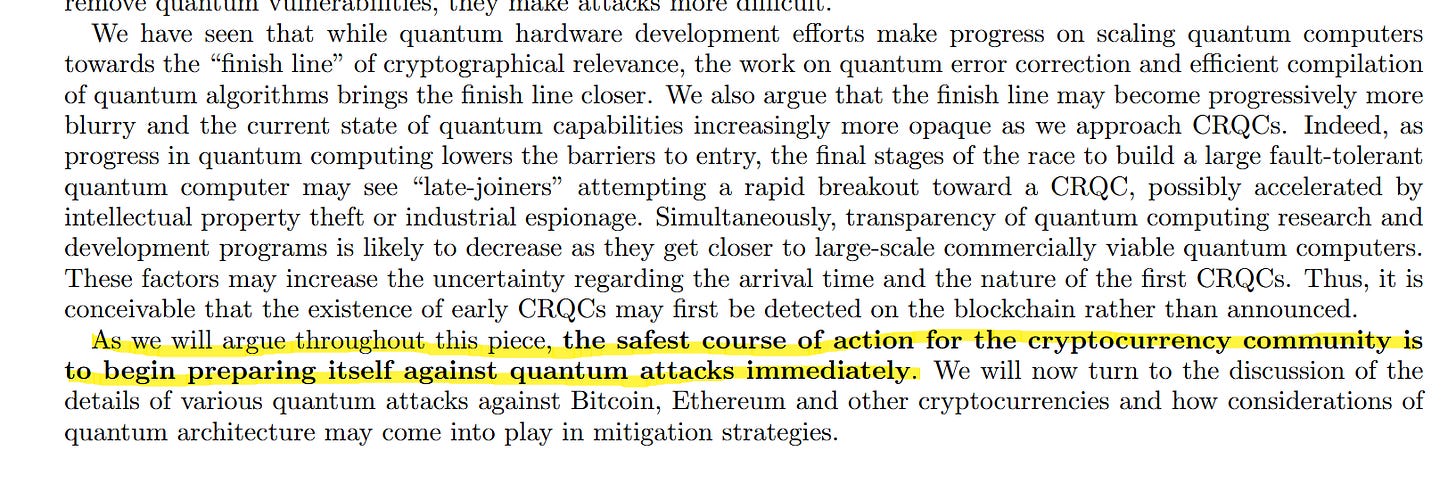
The core message of the Google Quantum AI whitepaper is straightforward. The resources needed to break cryptocurrency cryptography are far lower than we thought. And the gap keeps closing.
Bitcoin isn’t getting broken today. A 500,000-physical-qubit quantum computer doesn’t exist yet.
That said, it’s worth stepping back. The entity publishing this paper is Google Quantum AI. Google has one of the largest quantum computing research organizations and infrastructure bases in the world, and demonstrating the practicality of quantum computing is literally this team’s reason for existing. In other words, there’s no incentive for them to underestimate the threat. On the flip side, emphasizing the threat also helps justify quantum computing investment and drives PQC transition demand. Worth keeping in mind.
And the crypto ecosystem isn’t sitting still either. Cryptography is evolving in parallel with quantum hardware. NIST has already finalized PQC standards (ML-KEM, ML-DSA), the Ethereum Foundation has 8 years of PQ research behind it, and there’s strong mathematical backing that lattice-based and hash-based cryptography remain hard even for quantum computers. The quantum threat is real, but this isn’t a “one-sided race.” Attack and defense are co-evolving, and the outcome depends on who prepares faster.
The thesis the paper hammers home throughout captures this article’s conclusion: “The safest course of action for the cryptocurrency community is to begin preparing itself against quantum attacks immediately.”[1]
Distributed networks can’t update with a single switch. Banks can quietly swap cryptographic infrastructure, but blockchains are bound by transparency, immutability, and social consensus. Preparation takes years. Those years start now.
References & Sources
[1] Securing Elliptic Curve Cryptocurrencies against Quantum Vulnerabilities: Resource Estimates and Mitigations — Google Quantum AI original whitepaper (March 30, 2026)
[2] Quantum-resistant tokens jump 50% as Google flags risks to Bitcoin security — CoinDesk, coverage of QRL/CEL surge (April 1, 2026)
[3] Google Willow quantum chip — Google official blog, Willow 105-qubit processor announcement
[4] Google warns five quantum attack paths could put $100 billion on Ethereum at risk — CoinDesk, analysis of Ethereum’s 5 vulnerabilities (March 31, 2026)
[5] Quantum Computing Companies In 2026 — Quantum Zeitgeist, comprehensive company profiles (February 2026)
[6] PsiQuantum Announces Omega — PsiQuantum official announcement, Omega chipset + GFS Fab 8 manufacturing (February 2026)
[7] PsiQuantum Raises $1 Billion — The Quantum Insider, $1B Series E coverage (September 2025)
[8] Xanadu Becomes First Pure-Play Photonic Quantum Computing Company to Go Public — The Quantum Insider, Xanadu SPAC listing (March 27, 2026)
[9] Toronto quantum company Xanadu set to debut on TSX, Nasdaq in SPAC deal — Yahoo Finance Canada, Xanadu listing details (March 25, 2026)
[10] Xanadu and Tower Semiconductor Deepen Strategic Collaboration — Tower Semiconductor official press release, expanded SiPh collaboration (February 19, 2026)
[11] Xanadu and imec partner to develop photonic chips — imec official release, SiN wafer partnership (August 2021)
[12] Xanadu Announces A Quantum Computing Collaboration With Applied Materials — Canadian Manufacturing, TES detector 300mm process collaboration (May 2025)
[13] How is NVIDIA ‘Betting’ on Quantum? — The Quantum Insider, NVentures quantum investment analysis (September 2025)
[14] NVIDIA Introduces NVQLink — NVIDIA official newsroom, NVQLink announcement
[15] 2025 is the year of quantum computing — Constellation Research, Jensen Huang comments and quantum industry trends
[16] Ethereum Foundation Unveils Post-Quantum Threat Roadmap — The Market Periodical, pq.ethereum.org roadmap coverage (March 26, 2026)
[17] Watch out Bitcoin devs. Google says post-quantum migration needs to happen by 2029 — CoinDesk, Bitcoin vs Ethereum PQC response comparison (March 28, 2026)
[18] PsiQuantum Expands Development Engagement at SkyWater’s Minnesota Fab — SkyWater Technology IR, expanded PsiQuantum 200mm SiPh collaboration (May 2023)
[19] SkyWater CEO Calls Company ‘Quantum Foundry’ — EE Times, SkyWater quantum foundry strategy (November 2025)
[20] ‘Bitcoin cracked in 9 minutes’: BTC bulls scramble for post-quantum protection as Google drops bombshell paper — CoinDesk, industry reactions from CZ, Nic Carter, Eli Ben-Sasson, and others (March 31, 2026)
Disclaimer: This article is an independent, engineering-driven technical analysis published by PhotonCap. All content is based on publicly available information and is intended for educational and informational purposes only. Nothing herein constitutes a recommendation to buy, sell, or hold any security. The author may hold positions in securities discussed and may transact at any time without notice. Readers should conduct their own due diligence before making any investment decisions.



Bullish quantum